An Ubuntu server is a server operating system. It was developed by Canonical and open-source programmers. The Ubuntu system can run many things from websites, FTP, email servers, cloud servers, databases, and much more. The minimum requirements needed are the following:
- Ram: 512 MB
- CPU: 1GHz
- Storage: 1GB disk space
Installing Ubuntu Server
With the requirements out of the way, here is how to install and safely secure an Ubuntu server:
Step 1: Boot the Install Media
Step 2: Use the Installation Wizard to guide you through the process
Step 3: Choose your language

Step 4: Choose Your Keyboard Layout

Step 5: Choose Your Network
You can either configure it manually or auto-configure it if you have a DHCP server, otherwise, continue without network configuration for now.

Step 6: Configure a proxy server (if it is required)

Step 7: Specify an alternate mirror to get installations packages from

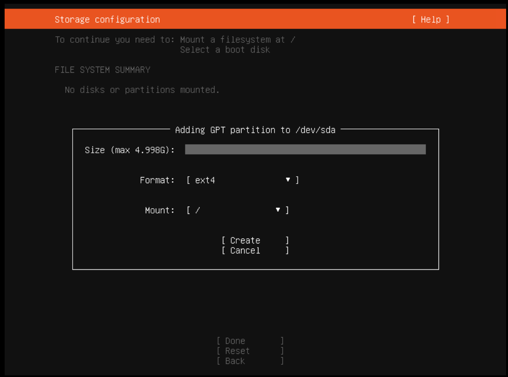
Step 8: Storage Configuration

Since our disk is a small 5GB one, automated partitioning will not work. Instead, we are going to manually partition this. First, select the disk under the device, partition it, and assign it as the “root” or “/” partition – where Ubuntu will reside.




Step 10: Set up one profile along with a password and hostname

Step 11: Software Installation
Here it asks if you want to install the OpenSSH package. This enables you to connect to the server after the installation if the network is configured.

Step 12: Install & Reboot
This screen shows the Ubuntu install in progress.

Once it is installed, reboot the server.


Now the version of Ubuntu and the version/sub-version of the packages used in it would depend on the ISO used. Normally, we find this could generally be a week or two old compared to the latest download. As long as your server is configured to a network, you can easily install the recent Ubuntu installation with a couple of commands:
– sudo apt-get update
– sudo apt-get upgrade
Securing an Ubuntu Server
Security on any server is key to the integrity of the data that is stored on it. We will cover some of the core essentials in hardening the Ubuntu server you just installed.
Updating Packages
Once the Ubuntu installation is complete, the primary task is to keep all the installed packages updated. This can be done by running a few commands that are provided by Ubuntu. After running these commands, you may or may not be prompted to do a reboot. Generally, this would update the Ubuntu kernel, and in such a case, a reboot is necessary.
# apt upgrade
# apt update
Custom SHH Port
On the Ubuntu server, we tend not to install a GUI, and managing the server is almost always via CLI. When these servers are remote, the only way to access them would be through SSH. Minimal installs generally will install the OpenSSH package, which uses the default configuration. This includes the port being the default “22”. This configuration is vulnerable to attackers hence it is best to change this as soon as possible. Fix this by editing the SSH configuration file at /etc/ssh/sshd_config. Once this is changed from the default to any custom unused port, restart the SSH service to bring this change live.
# grep Port /etc/ssh/sshd_config
Port 22
DISABLE DIRECT ROOT LOGIN AND ONLY USE SUDO FOR “ROOT” USER ACCESS
To disable the direct root login and only use Sudo for “root” user access, you follow similar steps as creating a custom SSH port. Complete this by modifying the OpenSSH config file and restarting the service after. But before this, create a new user and allow SUDO access. This can be done by the following commands:
# useradd cwhtechtips
# usermod -aG sudo cwhtechtips
# grep PermitRootLogin /etc/ssh/sshd_config PermitRootLogin prohibit-password
ALLOW ONLY TRUSTED IPS ACCESS TO SSH
SSH access is required typically only for configuring the server and managing the services on them. With that said, we recommend limiting SSH access to only a list of IPs that you trust. TCP wrappers are included by default with all Ubuntu installations and this helps filter SSH traffic. Enter the pre-determined trusted IP address in the /etc/hosts.allow file.
# sudo cat /etc/hosts.allow
sshd: x.x.x.x : allow
sshd: ALL : deny
The first rule allows the IP address (replace x.x.x.x with your IP address) SSHD access, while the second rule would be the default rule to block out all other SSH access. Finally, IP addresses would also be added with their own rule in a separate line, and make sure you enter this before the Deny rule.
Installing a Firewall
All Ubuntu installations come with a default firewall called UFW. But we like to use CSF (https://configserver.com/cp/csf.html) as well, because this provides additional functionality and makes it easier to manage. To install CSF, the following commands are ran
# sudo apt install iptables libwww-perl
# wget http://download.configserver.com/csf.tgz
# tar xvzf csf.tgz
# cd csf
# sudo sh install.sh
Once it’s installed, you will be running it in demo mode. To make it live, edit its configuration file at /etc/csf/csf.conf and modify the following line and set it to “0” to disable the testing mode.
# sudo grep TESTING /etc/csf/csf.conf
TESTING = “0”
Restart the service to make the change alive. Use the following command to restart it:
# sudo csf -r
Overview
Now you have the complete guide on installing and securing an Ubuntu server. Though securing a server also depends on the other services/packages installed, a solid security foundation has been installed. By implementing these tweaks/changes, the preliminary hardening of your server is complete and you are ready to put your Ubuntu server to use.


3 thoughts on “Best Way to Install and Secure an Ubuntu Server”